Samsung’s upcoming foldable device is on the way, but Google is already leading in several important aspects.
Comparison between Samsung Galaxy Z Fold 8 and Pixel 10 Pro Fold: Samsung’s Future Release vs Google’s Premier Product
Stripe and Airwallex, Once Acquisition Contenders, Now Competing Against Each Other
For most of its life, Airwallex and Stripe have mostly operated in different geographies, selling to different buyers. That’s changing.
Today’s Moon Phase: April 18 Moon Appearance
See the Moon phase expected for April 18, 2026 as well as when the next Full Moon is expected.
Hints and Answers for Hurdle on April 18, 2026
Hints and answers to today’s Hurdle all in one place.
Wordle Today: Clues and Solution for April 18, 2026
Here’s the answer for “Wordle” #1764 on April 18 as well as a few hints, tips, and clues to help you solve it yourself.
NYT Strands Clues and Solutions for April 18, 2026
The NYT Strands hints and answers you need to make the most of your puzzling experience.
Today’s NYT Connections Hints: Clues and Answers for April 18, 2026
Connections is a New York Times word game that’s all about finding the “common threads between words.” How to solve the puzzle.
NYT Pips Clues and Solutions for April 18, 2026
The New York Times’ latest game, Pips, brings domino fun to your desktop. How to play Pips as well as hints in case you get stuck.
Today’s NYT Sports Connections: April 18, 2026 – Hints and Answers
Connections: Sports Edition is a New York Times word game about finding common sports threads between words. How to solve the day’s puzzle.
Conclusive Engineering’s KSTR-SAMA5D27: Ultra-Compact, Low-Power SBC using Microchip SAMA5D27 SiP – CNX Software
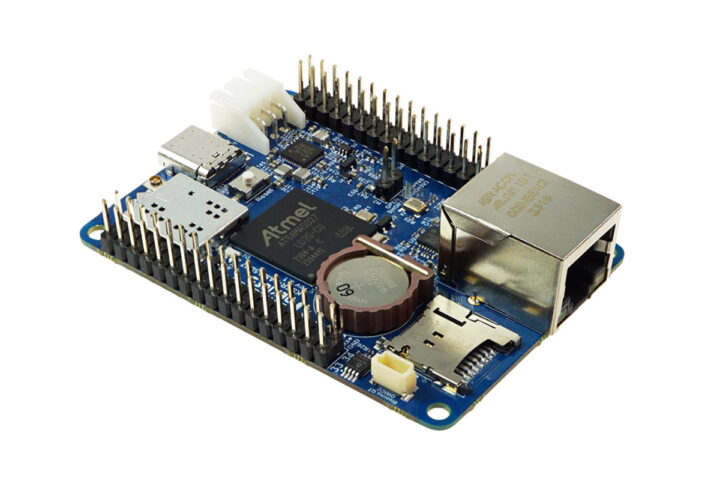
Conclusive Engineering KSTR-SAMA5D27Â is an ultra-compact (70x50mm) single board computer (SBC) powered by a Microchip SAMA5D27 Arm Cortex-A5 processor microprocessor clocked at 500 MHz paired with 256MB LPDDR2 (system-in-package). The board also features a microSD card slot and EEPROM for storage/configuration, Fast Ethernet, WiFi 4, and Bluetooth 4.1 connectivity, a USB-C port, two GPIO headers, and supports USB and battery power. It’s designed for IoT devices, smart systems, and edge computing applications. Conclusive Engineering KSTR-SAMA5D27 specifications: SiP –Â Microchip SAMA5D27 CPU – Arm Cortex-A5 microprocessor @ 500 MHz System Memory – 256 MB LPDDR2 Storage MicroSD card slot 4KB EEPROM Networking 10/100Mbps Ethernet RJ45 jack 2.4 GHz WLAN IEEE 802.11 b/g/n and Bluetooth 4.1 USB 1x USB 2.0 OTG Type-C connector 1x USB 2.0 Host on expansion header Expansion 34-pin and 30-pin connectors 2x Flexcom (configurable: I2C, SPI, UART) I2C 6-channel ADC with Vref 10-bit ISC (Image Sensor Controller), 10-bit […]
The post Conclusive Engineering KSTR-SAMA5D27 is an ultra-compact, low-power SBC based on Microchip SAMA5D27 SiP appeared first on CNX Software – Embedded Systems News.










